By Oiwan Lam
A police report leaked last week from China’s Xinjiang province describes Internet censorship circumvention tools as “second class violent and terrorist software.”

The leak raises serious questions about the consequences of using VPNs, web proxies and other tools that help Internet users get around censorship and other obstacles (like slow speeds) in online networks. While some companies offering these services are banned or disrupted in China, others are fully licensed to operate. It has been estimated that 1-3% of China’s internet users use circumvention tool to visit overseas websites.
The leak, which was firstly appeared on mainland Chinese social media but deleted quickly, has made waves in a number of overseas Chinese news outlets, prompting widespread concern about the legalities of using such tools. As one user on Reddit put it:
I understand this isn’t in all of China but if I travel to China with a VPN already installed on my laptop could I technically get arrested?
The report (below) was filed by a prefecture police inspection team on October 13 in Changji City, a Muslim autonomous area in Xinjiang, where the majority of population belongs to the politically marginalized Uyghur ethnic group. The report is to seek help from the county-level police to follow up on the case.
According to a report from Solidot.org [original post was deleted, content has been republished on Letscorp], the circumvention tool described in the report is a VPN (virtual private network), which allows users to access censored websites. The report calls it a “violent and terrorist software”.
Filed under the category of “online violent and terrorist acts,” the report’s subject line reads: “a netizen in Changji city is suspected of downloading violent and terrorist circumvention tool.”
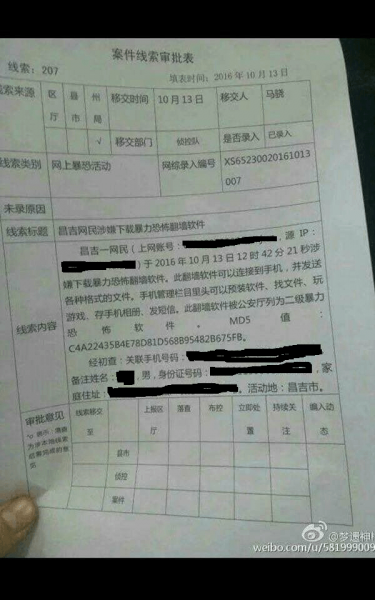
The descriptive text of the report reads as follows:
A netizen in Changji (online account number: XXXXX IP: XXXXX) is suspected of downloading a violent and terrorist circumvention software at 12:42:21 on October 13. The software can run on mobile for sending different types of documents. Once installed, the software can be operated on the mobile management tool set for searching documents, games, backing up photos and sending text messages. This software has been classified by Public Security Bureau as second class violent and terrorist software.
Initial inspection: Phone number: XXXXX, Name: XXXX male, ID number XXXXX, Home address: XXXXX Active in Changji city.
The exact downloading time marked in the “crime report” suggests that the suspect’s communications have been under surveillance for irregular online activities. The report does not describe any actual crime taking place, but rather it anticipates a crime merely because the suspect attempted to access censored web content with a circumvention tool.
Judging by the “function” described in the case report, the circumvention tool is merely giving its user access to overseas search engines and cloud storage. While the document specifically says that the circumvention tool has been classified by the public security bureau as a type of “second class violent and terrorist software”, there is no public information describing how it was classified as such, or what other products share this classification. This leaves Internet users with no way to know if their software or other tools are legal or not.
Targeting an ethnic minority region for VPN use
This is not the first time that Xinjiang police have targeted netizens who use circumvention tools.
Since the terrorist attack that killed 29 in Kunming Station in early 2014, government leaders in Xinjiang have begun to cast blame on circumvention tools for the spread of violent and terrorist messages. In 2015, Xinjiang residents were told that the use of VPNs would lead to the suspension of mobile phone services. In some cases, the netizens have had to report to the police in order to restore suspended mobile connections.
As former Xinjiang Communist party chief Zhang Chunxian put it:
90 percent of terrorism in Xinjiang comes from jumping the wall. Violence and terrorism keep happening due to the videos on the internet.
Zhang’s mention of “jumping the wall” refers to the use circumvention tools like VPNs to access overseas sites blocked by China’s domestic network filter, the so-called Great Firewall.

Though Chinese authorities have attempted to crack down on unlicensed VPN services, particularly when political tensions run high, use of VPNs is still fairly common in China. Institutions and corporations with overseas links have to rely on VPNs to connect to their business clients and partners. Even the Chinese authorities sometimes encourage their online civilization armies to circumvent the Great Firewall in order to influence certain political events such as the Taiwanese presidential election in 2015.
Online, some have expressed optimism that the labelling of circumvention tools as violent and terrorist software will remain limited to Xinjiang. As an American expat pointed out on Reddit:
As an American living in China for the past 2 years, I call bullshit. Everyone here uses a VPN. Even Chinese people who work for international companies use them. It’s openly talked about. I have a VPN for my work to access my email, google, and youtube. I have a personal VPN for my home computer. I have one installed on my phone to get on facebook. I do it openly in public and no one bats an eye. I agree with other comments about this only being in Xinjiang, but I’m guessing there were other problems happening as well. Bottom line, no one is really afraid to use VPNs in China.
This is certainly the case in much of mainland China right now. But a source from the China Electronics Technology indicates that these pre-crime surveillance software, among other “anti-terrorist” technologies, are simply being tested in Xinjiang and Tibet, and will later be introduced throughout the country. Once passed, China’s pending draft cybersecurity law may provide a firm legal basis for unrestricted access to user information online and facilitate the nationwide launch of such techniques.
Surveillance of “pre-criminal” activities
The leaked document also provides more details about the development of pre-crime technology and crime prevention enforcement in China.

As reported by Bloomberg in March 2016, the Chinese government began investing in pre-crime detection technology in 2014. A major antiterrorism technology development project which had an operating budget of US $25 billion was contracted out to a company called China Electronics Technology. The company’s engineer told Bloomberg that:
…he said the software would be able to draw portraits of suspects by cross-referencing information from bank accounts, jobs, hobbies, consumption patterns, and footage from surveillance cameras. The program would flag unusual behavior, such as a resident of a poor village who suddenly has a lot of money in her bank account or someone with no overseas relatives who makes frequent calls to foreigners.
According to this logic, a person with no overseas business using circumvention tool to communicate with people outside the country can be viewed as suspicious. And in the case of Xinjiang, where the authorities see 90% of the violent and terrorist crimes are related to getting access to censored information, detecting the downloading and usage of circumvention tool is part of the pre-crime crackdown.
China’s new anti-terrorism laws, which went into force in January 2016, have empowered the authorities to gain access to bank accounts, telecommunications, and a national network of surveillance cameras called Skynet. The leaked document suggests that the use of circumvention tools may also be documented as part of this program.
On China’s Twitter-like Weibo, a Chinese public security agency boasted about its success in pre-crime crackdowns:
[mks_tabs nav=”horizontal”]
[mks_tab_item title=”Translation]
Last year, Chinese homicide rate is 0.7 case in 100,000 population. The figure is similar to Switzerland, the safest country in the world. 98% of the violent and terrorist incidents have been deterred at the pre-crime stage. Either in day time or at night, you can feel safe walking in this land. This is something that many other western countries cannot accomplish.
[/mks_tab_item]
[mks_tab_item title=”Original Quote”]
去年,中国的杀人案每10万人0.7起,与世界上最安全的国家——瑞士相当;98%以上的境内暴恐事件,都在萌芽阶段就被警方打掉了。一个最直观的体验是:无论白天黑夜,你脚下的土地,几乎都可以让人安心漫步。这是很多西方国家做不到的。
[/mks_tab_item]
[/mks_tabs]
While the pre-crime indicators would likely vary from region to region, it appears that both the law and technology will soon be working in sync to watch Chinese netizens, in the name of crime prevention.
